Cisco Prime and Wireshark Advantages and Disadvantages
Introduction to
Networking Tools
Cisco Prime
Cisco Prime (formerly known as Cisco Works) is a network management tool that is Cisco proprietary. Prime is used for management such as monitoring, troubleshooting, configuration and administration of a network. This software allows for simpler control of the network. The monitoring and troubleshooting feature allows the network admin to immediately find and repair issues that arise throughout the network.
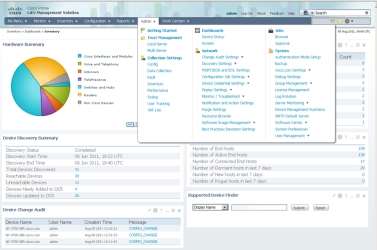
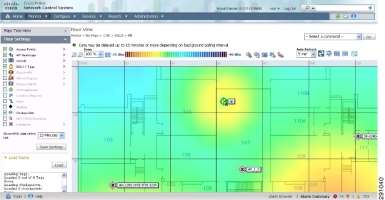
In the image above, you can see the home screen of the Prime software. It contains important information such as the types of hardware within the network. As seen in the ‘Admin’ section, the network administrator has access to network settings such as monitor and troubleshoot, notification settings, config settings, and much more. The GUI (graphical user interface) is very simple which makes it very easy to navigate through the settings. This is a useful layout for the admin as they can monitor the network with ease. You can also see a heat map of a building that uses Cisco Prime, the colours indicate the devices that are being used in the building, in the image we can see wireless access points.
Advantages of using Cisco Prime:
- Allows for easier monitoring and troubleshooting
- Easy to understand and navigate the software which will increase productivity
- Real-time information about areas in the network
Disadvantages of using Cisco Prime:
- Cisco proprietary, won’t work for hardware from other vendors
- May be expensive
Wireshark
Wireshark is a software that analyses packets sent throughout a network. It will display each packet and the details within the packet. Network administrators use it to analyse the network and to troubleshoot an issue if they see a problem. Wireshark has many capabilities, some of the key features are that it can catch packets in a real-time network. It can also save packets and the packets are laid out on a very clear GUI. Network admins can use Wireshark to identify and troubleshoot problems throughout the network by searching through the packets.
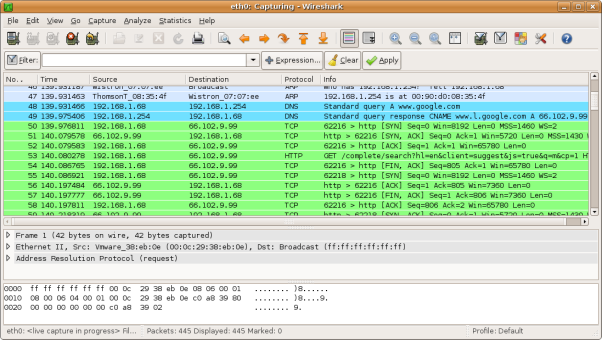
As you can see in the image above, this is what Wireshark looks like in a live network. We can see packets travelling through the network from the ‘Source’ and ‘Destination’ addresses. The ‘Protocol’ column shows us which protocol is being used within the packet and further information about it. This is extremely useful for network administrators as they can clearly see the packet in detail and easily identify a problem.
Advantages of using Wireshark:
- Free software
- Available for multiple platforms – Windows & UNIX
- Can see detailed information about packets within a network
- Not proprietary can be used on multiple vendors unlike Cisco Prime
Disadvantages of using Wireshark:
- Notifications will not make it evident if there is an intrusion in the network
- Can only gather information from the network, cannot send
I will be interrogating a network and I will report my findings. I will be testing the devices in the topology and check if they can all communicate with each other. In the topology below, you can see that there are three sub-networks.
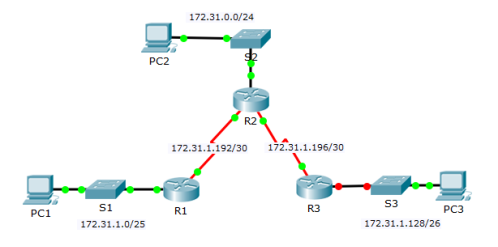
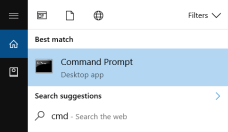
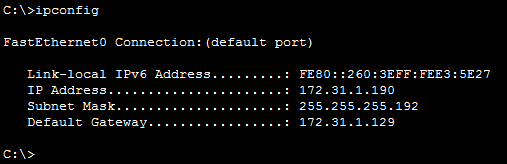
Firstly, I will be testing communication between the separate networks in the topology. I will be attempting to access PC3 from PC1. To do these I will access the Command Prompt from PC1. To access this, go to Start > search ‘cmd’ or ‘command prompt’ in Windows 10. Once you have opened the command prompt, you will come across a black screen. To find out the IP address, subnet mask and default gateway you should issue the ‘ipconfig’ command.
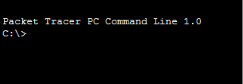
PC1 output above
The output above is from PC1 on the 172.31.1.0/25 network. I will now need to check the IP address for PC2 and PC3, I will be doing this because if I can successfully ping those two host computers that means all the networks are connected to each other and can communicate.
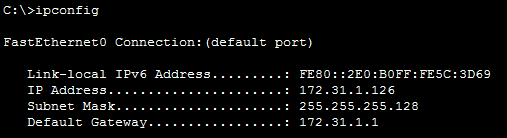
PC2 output above
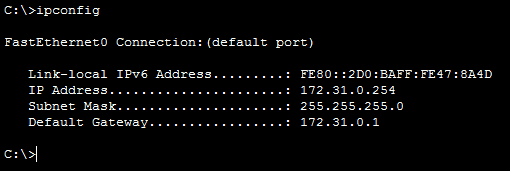
PC3 output above
Now that I know the IP addresses for PC2 and PC3, I can now attempt to ping them from PC1 to check if they can communicate with each other. I issue the ‘ping 172.31.0.254‘ command on PC1 command prompt and as we can see below, the pings were successful. However, you may notice that the first ping timed out, that is because the packet sent an ARP request for the next-hop. The output shows us that PC1 is now able to communicate with PC2.
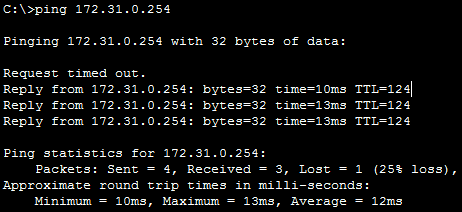
PC1 pings PC2
Now I will try to ping PC3 from PC1 to see if the hosts can communicate with one another. Again, just like PC1 to PC2, I will issue the ‘ping’ command along with the IP address of the PC3 host. As we can see in the output, the pings were unsuccessful. This means that the hosts cannot communicate with each other.
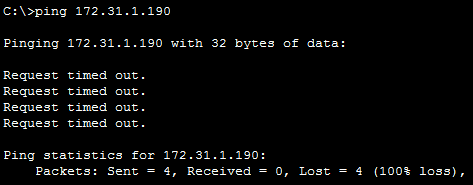
PC1 ping PC3
As we can see in the output below, I used the ‘tracert‘ command. This command is used to follow the path of the packet. What we learn from the command is that the packet times out at the 172.31.1.198 IP address. To troubleshoot the issue, I will locate the IP address and check the device connected to it.
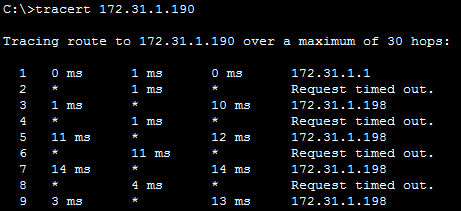
PC1 tracert to PC3
We know from the topology that R3 is connected to the 172.31.1.196/30¸and 172.31.1.198 is a part of this network. I will go into the router and check the interfaces to verify which interface it belongs to.

Router 3 in the topology
To do this, I will use a program called ‘PuTTY‘ and telnet into the router. Telnet is a networking protocol that allows a user to remotely access a device on the network. Once in the R3 router, I issue the ‘show ip interface brief‘ command. From the output, we can see that the interface that connects to the switch, GigabitEthernet0/1, is down. We know that this is the interface that belongs to the interface because the IP address of the GigabitEthernet0/0 belongs to the default gateway. The reason the PC cannot communicate with outside networks is because the switch’s G0/1 interface is down so it cannot forward the frame to the router.
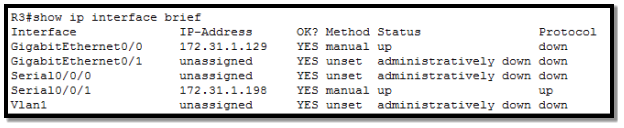
R3 output shown above
To tackle this problem, I will go into the configuration of the G0/1‘s interface and change the status from down to up. This enables the interface to communicate and process information. As we can see in the output below, I entered the configuration mode for the interface and switched it on. To verify, I will ping the PC1 host from PC3.
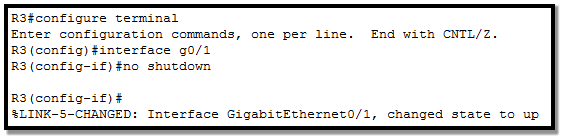
Enabling the G0/1 interface on R3
The pings were received successfully on R1. We have entered multiple devices in the networks and by doing this we have learned information about the network.
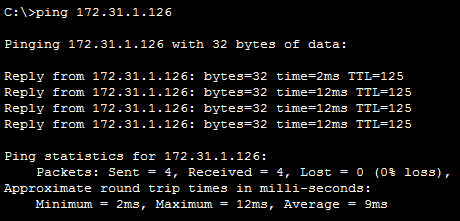
PC3 pings PC1
By using the command prompt I was able to find the status of the devices in this network.
This section will be about maintenance in a network that will need to be carried out frequently for the network to run efficiently.
In this section, I will be showing how to create and delete a user account on Windows 10. Firstly, from the Start menu go to ‘Control Panel‘ or alternatively, type ‘Control Panel‘ in the search bar.
Once it has opened, select the ‘User Accounts’ section. From that section select the ‘Add or remove user accounts‘ option. Once you have entered the next window, click on ‘Add a new user in PC settings‘ to create a new user. This will direct you to PC settings.


Now that you are in PC settings, select ‘Add someone else to this PC‘. This will require the new user’s email address or phone number to create an account with their Microsoft account.
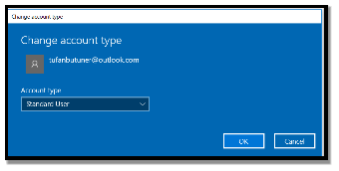
Once you have created the account, it will look like this. You will be presented with the option ‘Change account type‘ which will allow you to change the account type. You can give the user administrator rights or leave it as the default setting – standard user.
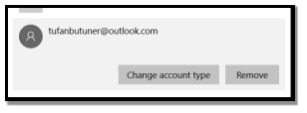
You can remove the account as easy as it was to create it. You can simply press the remove button.
There are many antivirus software applications that can be used. I have chosen ‘McAfee LiveSafe‘ to scan this PC. The interface is very simple and easy to use.
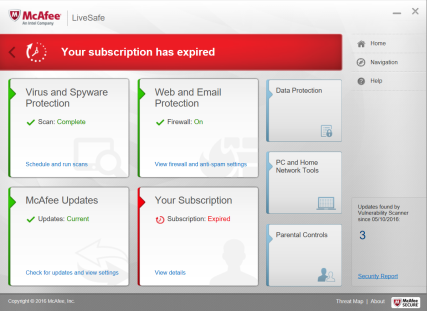
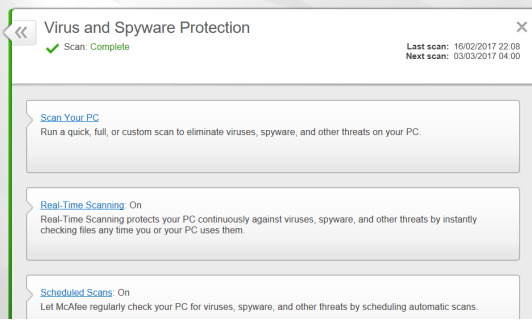
Firstly, I launch the application from the Start menu. Secondly, I click the ‘Virus and Spyware Protection‘ section. Within this section, you can see the date of the last scan and the next scheduled scan. This is very useful as it automatically does scheduled scans to protect your PC. To manually scan your PC, click the ‘Scan your PC‘ option. Once you click it, you can choose to run a quick scan, full scan or a custom scan.
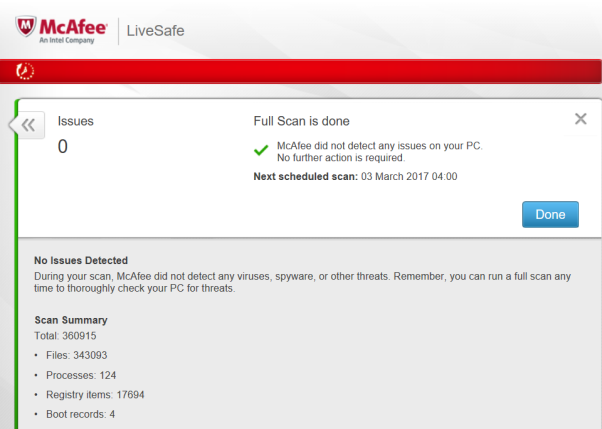
Once a full scan is done it will look like this. It outlines how many issues were found and how many files it searched. If any viruses were found it would automatically remove them from the PC.
Backup
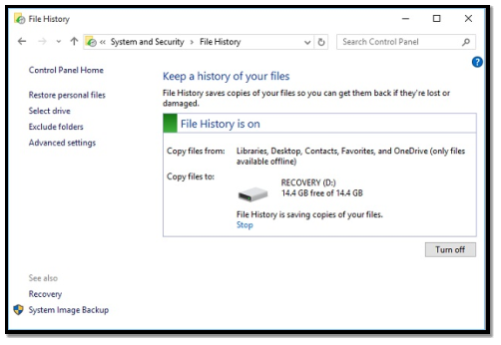
File backup is crucial for every PC because if any of the files become corrupt or are deleted, they will be saved. This is very important in businesses and personal computers as people must keep their files safe in case of any damage. This can be done very easily on Windows 10. Firstly, go to ‘Settings‘, then ‘Update & security‘, from this section there is a ‘Backup‘ section.


Once you are in the Backup section, click ‘More options‘ and select ‘See advanced settings‘.
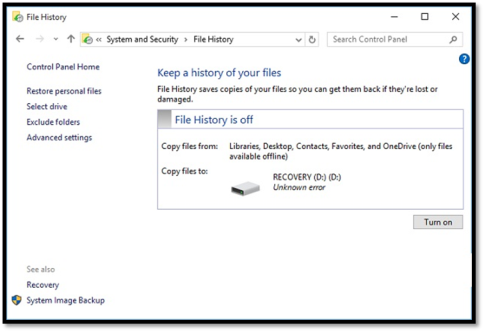
From the ‘File History‘ window, once you plug in an external hard drive, you can select a folder to backup from. This will then give you the option to select how often you want it to backup your files.
Restore
To restore a backup that you saved onto a hard drive, return to ‘File History‘ so you can restore your files using the ‘Restore personal files‘ option on the sidebar. Once it has opened you will be able to select the files you had backed up and restore them to a drive on your computer.
How to keep it secure
VPN access:
A VPN (Virtual Private Network) allows companies connect their branches from all over the world. VPN is a network used through the internet that allows a private connection between users. You can keep information within this network secure by configuring a password and encrypting it on both ends. This will not allow people to see what is going on in the network unless they have the password.
Firewall management:
The firewall is used to protect the network from viruses that could potentially enter the network. Firewalls are useful to stop unauthorised access