Network Physical Topology of ISP “TechnMaster”
 Network Physical Topology of ISP “TechnMaster”
Network Physical Topology of ISP “TechnMaster”
 ISP Infrastructure Physical Topology
ISP Infrastructure Physical Topology
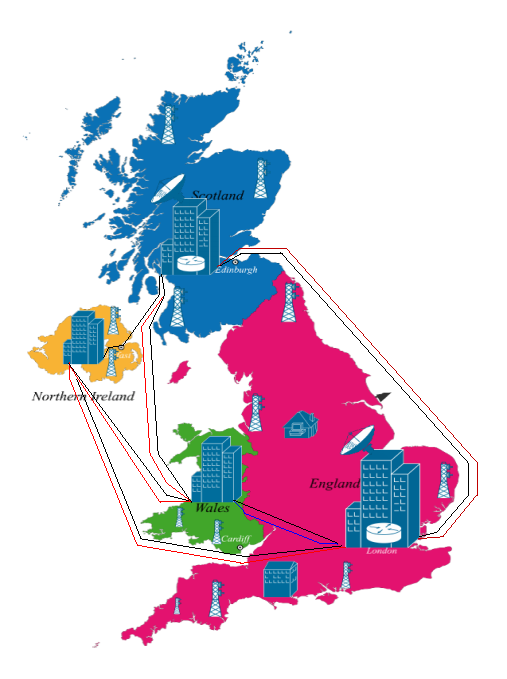
ThechMaster is the Uk leading virtual ISP (Interner and Services Provider), with it HQ in London where all main services and infrastuture and resource are located, the main secondary branche are locate in Scotland and have similar inftrasture as in london with some others branches around the country, in Wales and in NorthIreland that represent small branches and provide some on the server provided by HQ.
Internet Backbone (external) Infrastructure Diagram
Internet Backbone is a part of computer network located at the back-end connection between two different networks, strategically interconnect networks and core routers on the Internet, used for the large high speed and capacity between networks that are located remotely and transport very high volume of data.
 As the Internet high speed links it require high-speed bandwidth connections and high-performance servers/routers devices.
As the Internet high speed links it require high-speed bandwidth connections and high-performance servers/routers devices.
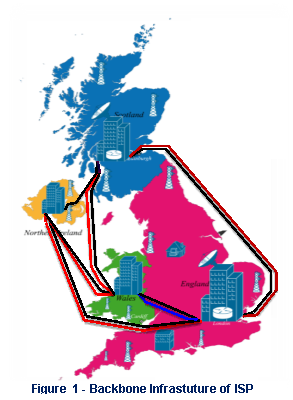
As one of the main service provided by ISP is the internet service, so prior to outline all the infrastuture network, the main backbone newtork of ISP are connected with other provider from diferentes continent by undersea fiber optic cable (Figure-3), as well as connection to other sub-region, inter-branches plus DC or transmition station that are related to ISP (Figure-2).
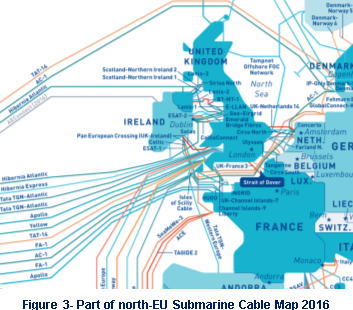
Moreover are the responsabilite of each ISP enterprise to take care or troubleshoot and more important reassure the operational of its termination part of fiber optic connection cable, even do some risck and threads are present independently of the location.
[1]As an Internet Provider Services that provide differente type of services (Cloud, Broadband, Telefone, VoIP, P2P Caching, IPTV, etc) the funtion and role of the bacbone is very crucial as it is the infrastuture that interconnects various segments of network, mainly in this case it provide all the principal data routes (Figure-3), between large, strategically and interconnected networks from different ISP (intercontinental) to and from our ISP core routers and internal infrastructure and vice versa.
 ISP Internal Infrastructure Diagram
ISP Internal Infrastructure Diagram
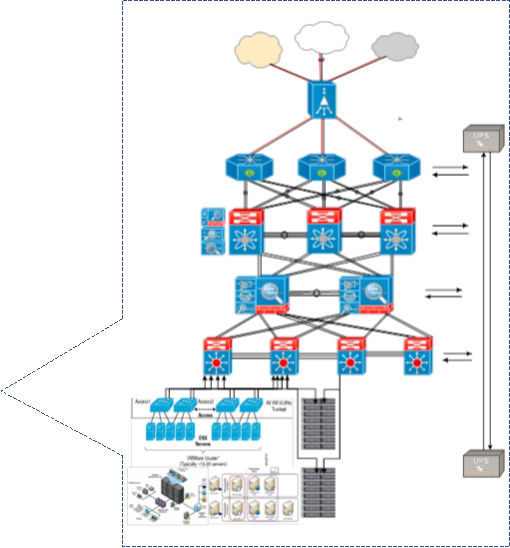
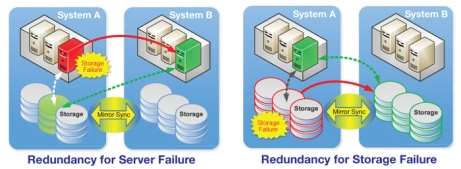
A robust and concise internal network and server infrastructures as the base and spine of all services is highly required to support ISP internal, external and remote services as well to provide at the highest level standards quality of all advertised type of service to the customers and business partner. As the business high requirement and demand the network spinal infrastructures (Netwwork, Server, CCTV, Access Control, Power Source and UPS, Phisical DR System and all subsystem) was designed with highly availability, elasticity and reliability in mind to overcame mainly 75-95% of any considered possible incident that could happen based on a preview and periodic Risk Assessment and Strategic Planning Processes delivery as one of the main police of ISP enterprice to assure its business continuity.
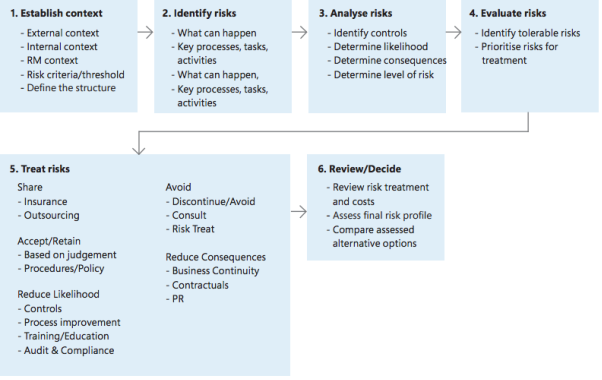
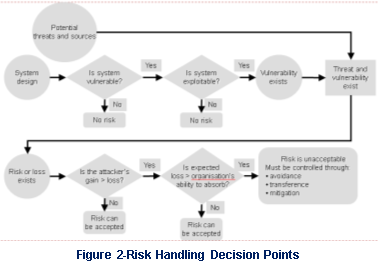 More over if have a look at spine network topology we can verify that at the bacbone device and after it for each connection more them one fiber cable sink is used to avoid fail, as well for realibility and better traffic troughput, this police and strategy is followed for the rest of the network as well on secondary inftrastuture system. Altought is not describet but it is clear from (figure 4) that for each infrastuture layer was takem is consideration all advice from report of RASP (Risck Assessiment & Stratgey Planning) team related of a list of Risk (natural or artificial) prior to design the all ISP infrastuture, to prevent lack of redundacny, avalibility, reliability or even elasticity, the RASP Risk Handling Decision Points guidince was takem in hight consideration.
More over if have a look at spine network topology we can verify that at the bacbone device and after it for each connection more them one fiber cable sink is used to avoid fail, as well for realibility and better traffic troughput, this police and strategy is followed for the rest of the network as well on secondary inftrastuture system. Altought is not describet but it is clear from (figure 4) that for each infrastuture layer was takem is consideration all advice from report of RASP (Risck Assessiment & Stratgey Planning) team related of a list of Risk (natural or artificial) prior to design the all ISP infrastuture, to prevent lack of redundacny, avalibility, reliability or even elasticity, the RASP Risk Handling Decision Points guidince was takem in hight consideration.
Risk Assessments/Management & Strategy Planning
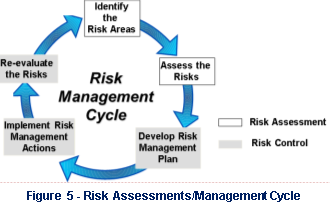 Techmaster ISP, as telecon enterprise that operate in highly demanding national and international market providing variety of tech service need to relay on its infrastuture as well on its human resource team capacity to deal and overcame all the possible threats and risck present daily and the RASP team is responsably to investigate and help creat or provide safe environment and soluction to help the company achive the point.
Techmaster ISP, as telecon enterprise that operate in highly demanding national and international market providing variety of tech service need to relay on its infrastuture as well on its human resource team capacity to deal and overcame all the possible threats and risck present daily and the RASP team is responsably to investigate and help creat or provide safe environment and soluction to help the company achive the point.
RASP help on the process to identifying, assessing and managing risks and uncertainties, affected by internal and external events or scenarios, that could restrain the ISP capacity to accomplish its methodology and key targets with a definitive objective of making and securing company and custumes value.
The RASP team conduct periodic and ocasional whem necessary the risk analysis involving risk identification, assessing the likelihood of the event occurring, and defining the severity of the event’s consequences. As well are they reponsability to conduct a interanl and external vulnerability assessment, which helps identify situations in which the enterprise may be putting itself at increased risk by not performing certain level of Security police.
As any other researche or assessiment the RASP as well condut with final comclusion and recomendadction based on the risk analysis results are summarized in a report to management, with recommended mitigation activities, some of the riscks, threats and vulnerability found and take in consideration by team are:
Risks, Threats and vulnerability associate to Internet Backbone infrastructure.
 As any other infrasturure the backbone area and device are not immune to riscks and threats, are they natural as earthquake, tsunami, or even human as theaf, intentional damange by undersea investigation veicule or other nachine, and deep sea fisher ships all those riscks mast be take in consideration, some of the risck and threts are:
As any other infrasturure the backbone area and device are not immune to riscks and threats, are they natural as earthquake, tsunami, or even human as theaf, intentional damange by undersea investigation veicule or other nachine, and deep sea fisher ships all those riscks mast be take in consideration, some of the risck and threts are:
- Undersea animal can bite and damage the fiber optic cable (figure-6).
- Rusting of the cover or protective layer of the fiber optic cable, because of the poor quality manifature (figure-6).
- Acidental or intentional cuting or damange of fiber cable by fish shipping or any other undersea machine.
- Acidental or intentional damange of infrastuture at the border end cable connection (sea-earth location), by criminal, curious, hacker, etc when not well safeguarded.
Risks, Threats and vulnerability associate to internal spine infrastructure and services.
The ability to anticipate opportunities and effectively respond to any risk or threats is critical for any company infrastructures, as it is no longer isolated by type of industry or geography location. Although it becoming more complex in nature and global in consequence, the rapidly capacity response to managing as well as mitigating risk and threats are a requirement to survival for company business continuity, driving a company’s into success of fail.
To assure the confidentiality, integrity, and availability of all the spine infrastuture, system and services components in the company the RASP, identiy and listed some of the main risk, threats and vulnerability that should be aware of :
- People awarnese (any one that can have access in to company are, guest, cusntumes or even trusted employees, etc)
- Access violation into restrited area (by unaoutorized persons)
- Natural Incidentes (earthquike, flooding, humidity, hight temperature, fire, air (dust) etc..)
- Absence or insuficient source of quality resource (Electricity, wather, fuel.)
- Hight restintion to all service provided and accessible by custumer even for roaming employee.
- All knowing and unknow cyber threat and attack, (DDoS Attacks, Direct SQL attack, Session Hijacking, Buffer Overflow, Port Scan, etc……..)
- Remote exploits (RAT, Trojan Horse, Bakdor, Worms, Trojans, Bots),
- Device Firmware and OS vulnerability, system out update, system and services missconfigured..
- Sniffing, spoofing, phishing, Social engieering, Port Scaning on border or any infrastuture devices, system
- Inadequately trained IT staff
- Intrusion, Hackers, theft (electronically and physically), Backup operators, etc…
Security Police to manage and mitigate any incident related to spine infrastructures.
As always, The confidentiality, integrity and availability of information, in all its forms, are critical to the on-going functioning and good governance of LSE. Failure to adequately secure information increases the risk of financial and reputational losses from which it may be difficult for LSE to recover.
Disaster Recovery plan to manage and mitigate any incident any incident related to spine infrastructures.
Cloud Citrix Infrastructure
We have Citrix Infrastructure in two collocations, Xen-Server 1 in Site 1 (Headquarter) and  Xen-Server 2 in Site 2 (Secondary Data Centre). Both Xen Server infrastructure is running under DMZ network as we have deployed Xen service for in house use only.
We have two major running service from XenApp and XenDesktop. The following architecture will elaborate each components of Xen server and how we have deployed it in our infrastructure.
XenApp and XenDesktop Architecture
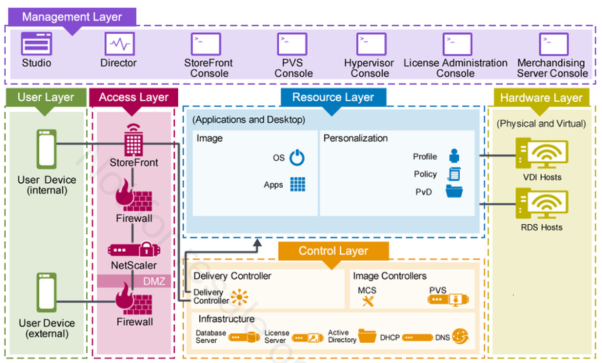
We have seven major components studios, director, store front console, pvs console, hypervisor console, license administrator console and machine service console to run Xen App and Xen Desktop in our infrastructure. To have access over the citrix environment users will require Thin Client or Thick Client Machine with citrix receiver.
Studios: Citrix Studio it is the main management console that enable us to manage, configure, deploy, eliminate the service. We have delivered application and desktop according to the application, processing, numbers of people associated and policy to the specific departments. We have hosted Windows Server 2012 R2, DataCenter Editions to each department so when they are getting citrix desktop session from windows server itself as it work on the shared environment.
Example:
In Support Department: We have hosted applications like putty, open ssh as the employee working in Support Department have to deal with the customer to check their internet connectivity and access other networking device and servers.
In Account Department: We have not delivered them putty and other networking application as they don’t use and it is not required for they. For the people working under account department we have delivered them accounting application like tally, excel.
Citrix Director: It is one of the major important components in the Citrix Xen application and desktop. Citrix Director is basically a web-based tool that helps the IP Support and Help Desk team to monitor and troubleshoot.
We have provisioned Administrative Privileged in each department Head of Department(HOD) where s/he can administrator each activity that the employee is performing. Even they can have the real time monitoring when the employees are dealing with the customer with some specified trouble ticket. We can even modify the role for the administrative user on monitoring using Citrix Group Policy.
The best thing on deploying Citrix Director is that if any of the customer is having problem with accessing certain portal or need help on dealing with some stuff then the person do not need to be physically there to solve the problem.
Example:
One of the employee from the Account Department have problem opening the web Brower and he call the IT Support Department for help. Back then before we deployed citrix in our environment one of the employee from IT Support Department had to be in the Account Department physically and try to solve the problem resulting high time consumption and delay in work as the employee must travel whereas using Citrix Director the IT Support Engineer and take shadow (Remote Desktop Connection) within the browser and start assisting. Even there are many different way of assisting user i.e text only mode where the IT Support Engineer will not be able to view the user desktop but will be able to assist him using text communication in order to maintain user privacy, next one is Shadowing in citrix technical term which is similar to remote desktop connection in two way one without write permission where the Support Engineer can view the user desktop and assist with the issue and the next one is IT Support Engineer and ask keyboard, mouse controller where the support engineer itself and take over and work on the issue.
Hypervisor: To share a resorudes of a device with multiple virtual machine for XenApp and XenDesktop we have Citrix XenServer using Citrix XenCenter to manage all servers.
Store Front: User will access to the specific web page which is hosted in IIS using store front according to the department on the browser where the users will be able to access to the specific delivered site using citrix reciver.
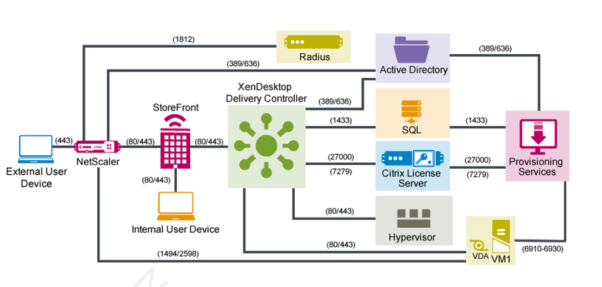
In the above figure we can see how user can access to citrix infrastructure. Here in the above figure a user is trying to access to provisioning services i.e. VDI or HSA first the user get to in the store front from NetScaler which is firewall that we have defined for Citrix Infrastructure the user will use Citrix Gateway then once he will get through the storefront which is basically URL the user will pass his username and password over the browser then the request will move other to the XenDesktop Deliver Controller where it will provide specific provisioned department then the request will further move to ADDS to check the user account name and password over the SQL to check weather it have the permission or not then finally it will check the citrix license server to check the license avalibality for the user if it’s form the machine it will check Device License and if it’s a user request than it will check the User License and then the user will get the session from the provisioning server.
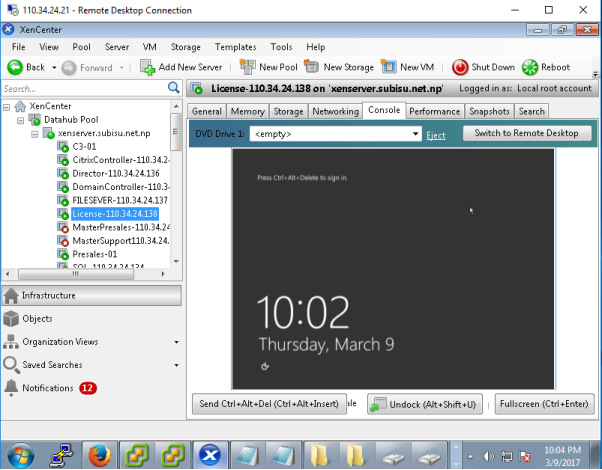
Figure: Pool of Xen Server 1 and Xen Server 2 with its components
We have deployed all these seven components individually; we could even deploy all seven components with in one singe Windows Server but at the end It will generate a lot of CUP utilization with the risk of single failure so we have deployed each component in each individual windows server so we have better performance and easy to manage. For Citrix Infrastructure on top of Windows Server Data Centre Edition 2012 and Mysql Server 2010 for managing database.
For users to access citrix we have deployed Atrust Thin Client device where, users will get login using Citrix Store Front on web browser where they will be required to pass their username and password. All the username and password will be managed by Active Directory in windows server.

Figure: Atrust T60 Model
Thin Client: User can have their Hosted Shared Desktop (HSD), Virtual Desktop Infrastructure(VDI), Hosted Shared Application (HSA) using thin client device like Atrust t60.
Thick Client: User can even access to the Hosted Shared Desktop (HSD), Virtual Desktop Infrastructure(VDI), Hosted Shared Application (HSA) using their own laptop machine or any end device like tables, cell phone.
Citrix Cloud Redundancy:
For Citrix Cloud Redundancy,
- Whole Citrix Infrastructure have been deployed in two major Site’s Site1 (Headquarter) and Site2 (Data Centre)

Figure: HP Blade Server Generation 9 with chasis
- Xen Server 1 and Xen Server 2 have been deployed in two blade servers in heart beat mode
- Both Xen Servers are in different colocation zone so if one goes down the service is provided from another source site 2
- KDC all the license associated with the Citrix and Windows services are within the Key Distribution Center in cloud so there is no change of getting access over the key physically or change the key.
- All the licensing service are monitored through Microsoft License Management Console
- All user or device license are monitored by the team of System Engineers where if anyone from the organization leaves or enrol they will update the license where the missuse of licensing is minimal
- Xen Server 1 and Xen Server 2 both service Xen App and Xen Desktop service license is only accessed by the Chef Technical Officer (CTO) hence, no other employee and stop the server license and if so there is always another license that can we up on from Citrix itself upon urgent request
Disaster Recovery Plan:
- Both Xen Server 1 and Xen Server 2 works in heart beat mode so if one goes down there is another server as a backup
- As blade server runs with in the chassis in case of any failure citrix service can be migrated immediately with zero data loss

Figure: HP MSA SAN 2040
- SAN storage have been configured with two controllers within itself Controller A and Controller B where if any array of SAS Drives goes down it will recover from another array.
- We have deployed dedicated SAN in each individual Site1 and Site2 where all the configuration and user data are stored. So, in this case even if one SAN goes down there is always another one so it’s 99.99% safe. Both SAN storage have been configured in RAID 1+0 mode for higher performance.
- In case of any disaster we have xen center from where we can manage each Xen App and Xen Desktop components. We have clustered both Xen Servers as a DataHub Pool name where we will be notified within the central management in case of any disaster.
- Xen Server 1 and Xen Server 2 both have been configured in our monitoring environment as well so if in case of any network failure our outage in the server we have notification in our monitoring application dashboard as well as it will be informed in the email along with the cell phone sms features. So if in case of any disaster in datacentre or if there is any failure in servers the team of system engineers can get into troubleshooting and response quickly.
- Both of our Data Centre Site1 and Site2 have passed ISO standard for building for data centre so if there is earthquake of 8.5 hector still our data centre will be operational and in case of fire we have advance fire prevention system.
- Power supply can be one of the biggest result of disaster, in our environment we have two power supply unit PDU A and PDU B (Power Distribution Unit) so there is always power supply to Xen Server Infrastructure if one goes down there is another one for continue power supply.
Threats Associated:
- According to the recent research the internal threat is increasing more than external threat.
- Citrix have its own threat control mechanisms and one of its components controlling threats is using Citirx Director.
- Citrix Administrator can monitor and keep log of each individual users, so every activity performed by the users are captured and monitored.
- As the Virtual Desktop is provided to user using Citrix provisioning service users will only get the access and permission to files and the application. Where the users cannot copy any data or file from anyone as we have defined permission to make change and view only its own file, so this reduce the threat of miss using information’s from one another or if any unusual actives are found performed by the user beyond their access then it will be reported by the system automatically hence can reduce threat.
- Each user activity is monitored using Director, for example if any of the user want to install any suspicious malicious code or application the citrix service will not allow them to do so if found then the Citrix administrator and take over the user session and eliminate the task.
- No any other application can be install in the Xen App or Xen Desktop other than those applications which are predefined by the citrix administration so there are no any threats associated with in this technology and the user they cannot make any comment on server.
- We have group of system engineers monitoring citrix infrastructure using Citrix Director so if in case of any unusual traffic or activities are seen it will act in an instant.
- All the Citrix request must past though Citrix NetScaler which is firewall and gateway for the internet traffic.
Policies:
- Citrix Xen App and Xen Desktop have over more than 3000 policies, where we have defined few from them
- Users can not access another department other than their own. For Example: Employee working for Account Department cannot access the IT Support Department.
- User only have read/write/delete policy with in their user account
- If user make mistake while passing their username password more than 3 times in a day, then it is suspected to threat or any unauthorized access hence the system will block the user itself. Or if it’s a genuine request then the user can make a request to change the username and password.
- Users user name and password authentication have been defined within the windows active directory with citrix policy
- Each department have its own printer so account department and not use IT department printer this policy have been deployed using Citrix UPS (Universal Printer Service)
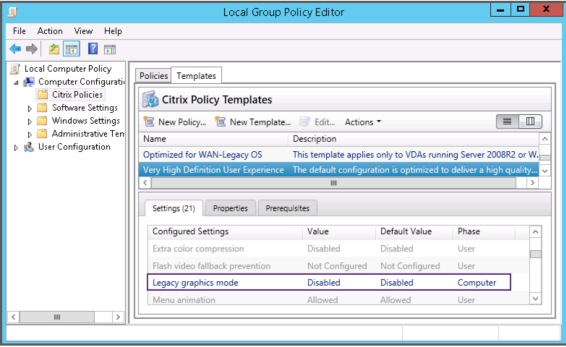
Figure: Defining Citrix Policy for Very High Definition User Experience
- In the above figure the Citrix Administrator have defined the policy for Legacy graphic mode which will enable user to feel real desktop like a physical desktop graphic.
ISP Different Department and Their Role
Level 1 (L1) – Support Department
Sub Category for L1 `Support Department
1. Technical Customer Support Department
* Technical Customer Support Department handle all the calls from the customer regarding different services that are provided by the ISP. Example: In our ISP our major business is bandwidth and Cloud Service so the our Support Team deals with all the trouble tickets related with the Cloud Service and Bandwidth i.e. a Customer want to have a VPS service over Vmware Exsi with some specific configuration they take the customer requirement and forward it to Level 2 – System Department.
2. Technical On Field Customer Support Department:
* Technical Support Engineers will go on site customer end to configure basic router along with the username and password provided by the L1 Customer Support Department for the Internet Connectivity.
Level 2 (L2) and Level 3 (L3) – Support Department
Sub Category for L2 and L3 Support Department
1. L2 System Department
* L2 System Engineers are responsible to maintain their internal running services and network that are interconnected along with the servers. To manage the running service we have different cloud platform Openstack, Exsi Vmware, Citrix. These department is more over with the operational task to all they need to take care is make sure all the service is up and running.
2. L3 System IP Engineering Department
* All the Research and Development is done in this department. If there is any new technology in the market this team will to research on it and work closely with the porcument and management team to further continue organization with the advance technology and good business.
1. L2 Network Department:
* This department is more over like l2 system department. They make sure all the internal and external network is operational and working fine. They are responsiable more in manageing internal network and if there is some basic configuration that is required to be done.
2. L3 Network IP Engineering Department
* This department is responsiable for doing research and development on existing top level network like core network. They are responsiable to test the new device and alanyse whether they are reliable and cost efficient or not for the organization.
3. Account Department
* Managing Company employee salary, customer billing
4. Project Department
* Bidding project brining new project
5. SPI Department
* Working with the CMTS network
6. NOC Department
* Monitoring Different Data Center network connectivity link and mainting all the servers and networking equipment with the data center
7. Enterprise Customer Department
* Dealing with the big size company
6. Retail Customer Department
– Dealing with the retail home user customers
Public Cloud:
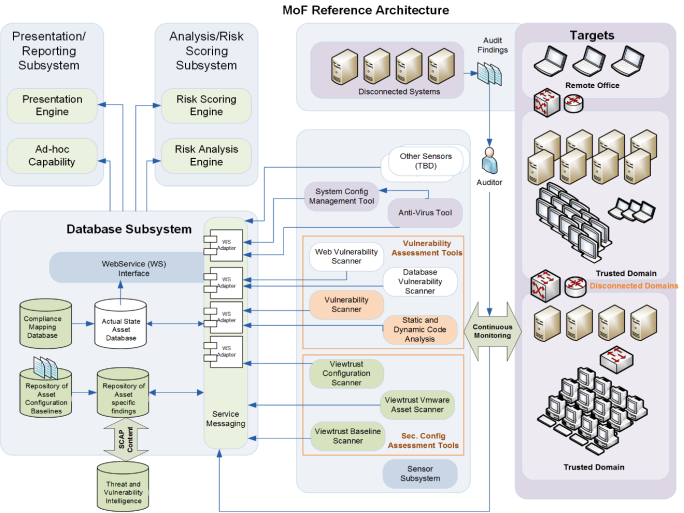
The Techmaster ISP offers a public cloud to the users where they can pay as you go model. The cloud has several payment options which are provided by the third-party gateway. These payments are Visa/ Mastercard and paypal. There are firewalls and risk management server on the public cloud. The risk management server is provided Viewtrust by Dell to manage the risks ingests all the data and logs. The below diagram explains the way the public cloud is setup:
Risk Management on Techmasters Public Cloud
The techmaster risk management department uses the ISO 31000 for risk management. The risks are evaluated and reviewed time and again. The below diagram explains how the risks are handled on different stages:
Due to the high rate of risk Techmaster has implemented the Risk management server which is used to ingest all the logs from the network and the servers online. There are several risks associated to the cloud. Below are the risks associated:
Risk Assessment Table for Public Cloud:
|
Score |
Rating |
Definition of risks |
Risks like-hood for Cloud:
|
Score |
Like-hood Rating |
Probability |
Frequency |
|
5 |
Expected |
90-100% |
Almost quarterly |
|
4 |
Highly Likely |
70-90% |
Yearly |
|
3 |
Likely |
50-70% |
Every 2 to 4 years |
|
2 |
Not likely |
10-50% |
Every 4 to 6 years |
|
1 |
Slight |
<10% |
Every 7 Years and Beyond |
Enterprise Risk Management Server:
Techmasters has a risk management server which ingest all the logs from the servers and presents it on different level. Viewtrust solution provides a scalable data ingest, collection, storage, processing platform which is currently supporting critical enterprise environments monitoring several devices and processing multitude of data input types from number of sensors as shown below. The Sensor sub-system collects data from multiple legacy and new sensors for collecting Hardware, Software, Vulnerability and Configuration information about assets within the enterprise. The Collectors are centralized and distributed to collect, process data close to the source. The data once processed is then sent to the warehouse for data normalization and transform using the Business Logic component of Viewtrust. This in turn results into a ‘Common Operational View’ of the data from multiple sensors. The following diagram depicts and describes the Viewtrust Risk Management Analytics with the continuous monitoring dashboard architecture:
Disaster recovery plan
Disaster recovery plan is one of the most important thing in managing a network. The reason for it is, when a disaster happens, there should be a proper plan in order to recover the network. So, every organization should have a proper disaster recovery plan with them.
What is a disaster?
Disaster is an event that can make great harms and damages. There are natural disasters and disasters which occurs because of human activities. Natural disasters can be floods, fires, earthquakes and etc. Because of these natural disasters, physical damages can be happened for the network. Non-natural disasters can be happened because of the events such as hacking network and denial of service.
Disaster recovery plan is the method which can be used to avoid these types of disasters. Disaster recovery plan helps to restart operations of a network after a disaster. Disaster recovery plan works with three methods to recover a network after a disaster. Those methods are,
- Restoring
- Recovering
- Replications and backups
According to the ISO 22301 standard for business continuity plan, the following things should be studied,
- Users, purpose and the scope :- here, the reasons for the need of the business continuity plan should be discussed and the objectives of it.
- Refence documents :- what documents that are relating to the business continuity (ticketing systems which contains the previous experiences of the troubleshooting of the system)
- Assumptions :- the prerequisites that need to exist in order for this plan to be effective.
- Roles and responsibilities :- here, the roles of the people in the organization and their responsibilities regarding the business continuity should be identified.
- Key contacts :- here, this should contains the contact details of the people who should be contacted when executing business continuity plan.
- Activation and deactivation of plan :- this stage decides where the plan should be activated and the methods of activating it and requirements of deactivating it.
- Communication :- this identifies the parties that have to contacted while a disaster happens and the people who are in charge of doing the communications.
- Incident response :- here, the things that have to done immediately after identifying the disaster are discussed. This can be helpful to reduce the damage to the system.
- Transportations and the physical sites :- this identifies the locations of the primary and alternative sites and the best possible transport methods in case of an emergency.
- Order of recovery for activities :- this lists all the activities with complete Recovery Time Objective (RTO)
- Recovery plans for activities :- this has the step by step information of recovering the system and interactions and interdependencies with the other steps of the recovering process.
- Disaster recovery plan :- this is the plan that has to executed when a disaster happened.
- Required resources :- this is a list of all the resources (employees, devices and services) that are required for a business continuity plan
- Restoring and resuming activities from temporary measures :- this describes how to continue the business by doing proper restoring processes when a disaster happens.
(Advisera, 2017)
Disaster Recovery Plan and Business Continuity for TechnMaster
Identifying the critical and vital information of the organization is the first task that should be done when creating a disaster recovery plan. Here, there are two main types of information with the TechnMaster. Those are, the information of the internet services and the information of the cloud services. For internet services information, TechnMaster has the information of three internet feeds and information of their customers. Here, TechnMaster has the information such as agreements with their internet feeds and their customers (Service Level Agreements). Here, TechnMaster should able to protect these data. Otherwise they will not able to continue their business properly. So, they maintain separate file servers to store them. With the cloud services of the TechnMaster, it allows authorised user to use service based on SLA as well Pay-as you go that the user bought from ISP such as Cloud service (virtual machines, Saas, Paas, broadband, etc). So, the users may install their software and save their important information on those virtual machines that are of all total user responsibility and the ISP responsibility relay on reliability, availability and maintenance of the infrastructure to provide all those service. So, these are critical information for the TechnMaster and they should able to protect them by having proper security and recovery plans.
After identifying the important information assets, recovery needs should be determined. Here, the file servers and the cloud servers (Xen servers and ESXI servers) should be backed up because those servers contain with the critical information for the TechnMaster. After identifying all the important information assets and determining the recovery needs, the development of the backup solutions and implementations of them can be done.
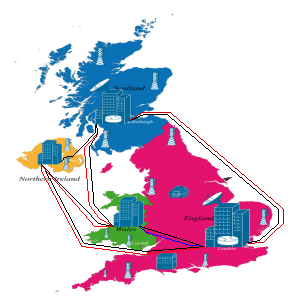 There are 4 branches of TechnMaster. Those branches are located in London, Wales, Nothern Ireland and Scotland. Headquarters of the TechnMaster is located in London. So, London branch has the control over the other branches of the TechMaster. And the London branch has more important with it as it is the head branch of the company. So, the information in the London branch has higher priority than the information in the other branches.
There are 4 branches of TechnMaster. Those branches are located in London, Wales, Nothern Ireland and Scotland. Headquarters of the TechnMaster is located in London. So, London branch has the control over the other branches of the TechMaster. And the London branch has more important with it as it is the head branch of the company. So, the information in the London branch has higher priority than the information in the other branches.
Figure 1
In the Figure 1, the geographical map of the TechnMaster is shown. As the London branch has more important information than the other branches, information of London branch is backed up in every other branch. So, if any disaster happens to the London branch, there are three copies of it in the other three branches. And every branch is backed up in the London branch.
There are three ways of backing up the system when a disaster happened. Those three ways are,
- Hot sites :- these sites are fully equipped and configured with the most up to date backups and ready for any immediate back up processes.
- Warm sites :- these sites are same to the hot sites but software applications are not fully prepared.
- Cold site :- only basic services and facilities are kept ready
So, according to these three methods of backing up, the branch in Wales is configured as a warm site. In the current situation of the world, a lot of organizations are using the warm site method for backing up their systems as it is easy to recover in a disaster and it is cost effective way of backing up. And also, Wales is the nearest branch to the London branch. So, in case of an emergency, people from London branch can arrive to the Wales branch easily than the other branches. So, they can save the time for travelling and as it is a warm site, they have some limited jobs to do in case of an emergency. In Northern Ireland branch and Scotland branch the London branch is backed up as cold site as they already have a warm site in the Wales. And all the other three branches are backed up in London branch as cold sites as it is the cheapest way of backing up and with the cold sites they will able to continue their business without any problem.
[1] http://submarine-cable-map-2016.telegeography.com/