Online Course for Phishing
Â
Applied Phishing
PROJECT in TI-ANS-ANS-TTC
Â
The report aims to provide an online course for Social engineering (phishing) for TTC students. The proposed course is designed based on the approach of research based learning. Proposed design of the circuit is supported by the theory. The report aims to provide an online course for “ICT” department. The expected result is to provide a new learning course for ” security information” Provide a new content, types, problems, solutions and how to informed about phishing technology.
 What is phishing? It’s technique used to steal personal information through spamming, fake websites, unofficial applications or other deceptive means, that’s means someone create a website which resembles original website 100% and the website which created asked for specific data such as request information entry or data update or add credit card and so on. So, this way is start by sending a message which similar to the message the original company and the content of message request to entry the link to update data, sometimes the link malicious files which help phishersto control device and steal data. To avoid Internet phishing, people should have knowledge of different types of phishing techniques and they must also be conscious of anti-phishing techniques to defend themselves from getting phished[1].
What is phishing? It’s technique used to steal personal information through spamming, fake websites, unofficial applications or other deceptive means, that’s means someone create a website which resembles original website 100% and the website which created asked for specific data such as request information entry or data update or add credit card and so on. So, this way is start by sending a message which similar to the message the original company and the content of message request to entry the link to update data, sometimes the link malicious files which help phishersto control device and steal data. To avoid Internet phishing, people should have knowledge of different types of phishing techniques and they must also be conscious of anti-phishing techniques to defend themselves from getting phished[1].
2.1. Phishing Techniques
2.1.1. Email / Spam
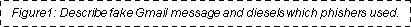
Phishing by using email or spam are most common phishing scam. Phishers can send the similar email to millions of users, requesting them to loading personal data. The information which are steal will used for unlawful ways. Most of the message have a note which ask users to enter the personal information to update and verify accounts. Sometime, phishers asked you to fill a form to access to a new services(Figure1)[2].
2.1.2.  Instant Messaging
Instant Messaging
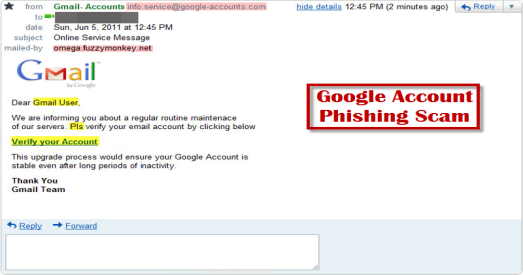
Instant messaging is one of the phishing ways which used by sending a message provide a link that direct user to fake website, that’s website are similar to the original website. So, If user don’t check the URL of this link, then he will fall on the phisherhand, sometimes it’s going to be hard to find out the different between the original and fake URL. Then, link contain form which phisher asked to fill(Figure2[3])[1].
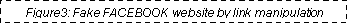
2.1.3. Link Manipulation
link manipulation is one methods that phisher use in websites by sending a link and when user click the link it will start to direct user to the phisher website instead website which in the link. The way to prevent link manipulation is to put the indicator of mouse over the link to check the real link(Figure3[4])[1].
2.1.4. System Reconfiguration
Phishers may send a message that asked the user to change the settings of the computer. The message might arrive from a web address which comparable an official source. For example: URL can be modified by phishers to direct victim to a fake websites. For example: a URL website of a FACEBOOK may modified from “www.facebook.com” to “www.facebo0k.com”[1].
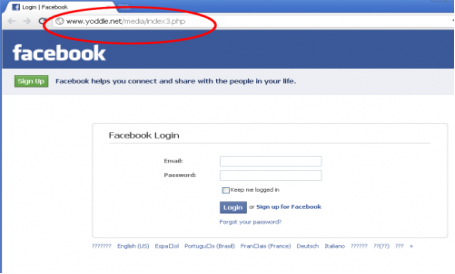
2.1.5.  Phishing through Search Engines
Phishing through Search Engines
This is one of phishing scams and that by using search engines which direct the user advertisement sites which may present low price products or services. So, when the user select some of these offers and begin to put data of the credit card, then it’s collected by the phishing site(Figure4[5])[6].
2.1.6.  Phone Phishing
Phone Phishing
The phisher may also used phone by making calls to random users and request them personal details about bank account or any others information and the phishing caller may be automated response. They may be friendly with you, start calling you by your first name and asking you about your family. They may act working in a company you trust and asking to update your accounts or asking for credit card. So, we see that kind of phisher have a little information about you before the call and after the call, they may get all the data they want to complete steal whole data.
2.1.7.  Malware Phishing
Malware Phishing
Phishing scams malware it’s one of the technique need to be run on the user’s PC’s. The malware is typically linked to the email sent to the user by the phishers. Once you get on the link, the malware will begin to publishing and causes damages inside PC. Sometimes, the malware attached to downloadable files.
phishing was spread around the year 1995, but they was not known to people until few years. So, this is negative point for people who does not take a careful and about the phishers because they maybe make a serious problems in one day. So, it is helpful to have a basic understanding of the behind them[7].
Most of the phishing scam are successful and that because people don’t know about scam methods which phishers use it. So, there are several ways to avoid to be a victim. We can get the idea about those list which may help to prevent phishers to steal your information and be aware about the following list:
- Keep Informed about social engineering techniques specially phishing techniques so that will help you to have an information about the methods scams that phishers use it and you know the ways to prevent all scams.
- Install an Anti-Phishing. So, a lot of popular Internet browsers can be Associated with anti-phishing toolbars. So, this is a common way to prevent the phishing through search engines or websites, anti-phishing toolbar can alert you from fake websites by blocking it. Such as AdBlock.
- Verify a site’s security: it’s important that websites you visit are security and free from fake advertisement and illegal products. So, keep informed about the website’s URL which should have to begin with “https”. Also, you should see an icon lock close to the address URL. Also verify the certificate of websites security.
- Verify your online accounts periodically as long as you don’t visit your online account for a long time, verify each of your online accounts periodically and changing your passwords regularly too. It’s good that each of your accounts has different password.
- Use best firewalls: you can use two option kinds: a desktop firewall and this is a software type install in your device, second is a network firewall this is a type of hardware which are in a routers or switches.
- Never Give Out Personal Information.
- Use Antivirus Software.
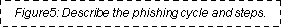
- Use an Alert Password from Google to alert you from phishing.
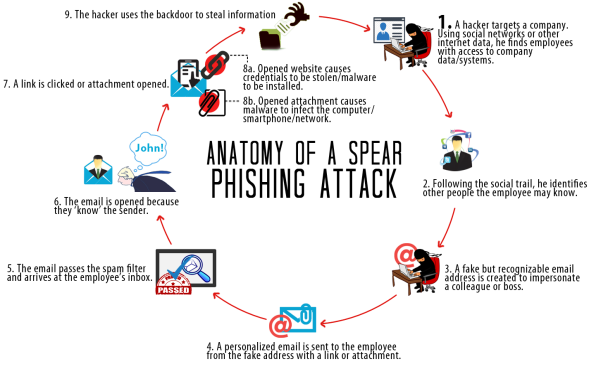 We see here in this figure5 the cycle of phishers witch they move with each steps when they target personals or companies. figure below will explain this cycle more(Figure5[8])[9]:
We see here in this figure5 the cycle of phishers witch they move with each steps when they target personals or companies. figure below will explain this cycle more(Figure5[8])[9]:
What do you think about your passwords. Do you use just one or simple to figure out variations on just one? If you do both, you shouldn’t, because you’re making it easy for a phishers to get access to your personal information. Every password for every site or different accounts should be different. Letters numbers and characters work best to keep password difficult and hard to get. Change them repeatedly. The special programs for internet security and system of device can help you to keep follow of your passwords.
Because Google are the famous company and has too many users, It’s important to set high level of security to protect users information. So, from the phishing side, Google has created a new tool which can secure users data from phishing. The main idea of this tool is to alert user when the password of account are entered in other original google.com. So, if user receive a message in e-mail and this mail are look like original webpage of Google and with a link asked you to change or update your password account. Then you click the link and start to direct you to another website and stealing your personal data. So, this tool from Google will alert you when personal data are entered in other Google account and trying to follow and show the suspicious signup page and alert you before you enter your personal data and password(Figurs6[10])[11].
There are several target in a phishing: the end users, businesses, the computer compromised to host fraudulent sites and the ISP hosting the email address. So, phishing want to get the important information from those to get all permission to control[12].
I think about the most common type of phishing technique are used is E-mail phishing so far. I chose that type because I see that in every news, TV, websites and social media. The last attacks which happen in Saudi Arabia in Jan 2017 by the virus which called SHAMOON by Green Big groups. This virus targeted most popular company in Saudi Arabia like ARAMCO and Communications and Information Technology. The virus was working for several attacks like send an E-mail to the employs of the ARAMCO company which include the malicious link and the message is similar to original messages of the company. Then, some of the employs are failed in this E-mails and the viruses are distribution and made a huge damage like stole information and delete all the data stored on the computers. So, I chose this type which is most common because of this story happened in 2017 and there is no way to stop it until we make a strengthen the defense of this attacks before happening[13].
Alic and Bob are the names used in scenario security characters. This names are chosen based on the letters of the alphabet (A)lic and (B)ob. Discoverer of this theory put names of people to make it easier to understand and study. If we suppose that Alic are sending a private messages to Bob by postal mail. Alic knew that postman are reading the message she sends. She thinking to find a way to send a message without anybody read it. So, Alic buys a lockbox and two keys (Encryption & Decryption) to open it and meet Bob to give one of this keys. Alic put the message inside this lockbox. The postman cannot read the message or open it or looking through the lockbox. So, after the message delivered to Bob, he can use the key to open the lockbox and read the message. So. Bob as well can use the same method to send a message to Alic and they are sure about the security message exchange and this is called a symmetric key encryption.
Let’s keep continuo with Alic and Bob. Now, Bob buy a new padlock which is open and put it with the message in the lockbox and keep the key of the padlock with him. Alic receive the lockbox and buy a similar padlock which Bob sent it with the message, and puts her message and the new key of her new padlock in the lockbox. Then. she locks it with the Bob’s padlock and send it to Bob. Now Bob can read the message and get the key of the padlock Alic’s. So, Alic and Bob can exchange messages as they want safety.
If we suppose that Alic are person (A) and Bon are person (B). A want to send a private message to B but person A discover that some person who is trudy are reading the private message when send it to B. So, A thinking about some method to encryption the message when send by add a code with so that message can’t opening and read until insert that code. Then, A send a message after give the code to B to decryption the message so he can read it and no one than A and B can decrypt the message because they have the same keys to encrypt and decrypt it. This method called encryption and decryption and the keys are called Symmetric-Key Encryption.
Let’s suppose that we have two persons Mohammed and Abdullah want to exchange encrypted messages so that no one can see it. Mohammed comes through a particular program (browser in case SSL) and produces two keys “associated with each other’s” one public key and the second are the private key. Mohammed then sends the public key to Abdullah by any method. Abdullah uses this key and encrypts the message that he has by the public key who sent by Muhammad public key. And then sends the encrypted message to Muhammad. Mohammed then decrypts the message code via the private key which is with him and associated with the public key. So, Muhammad can encrypt a message with the private key and Abdullah decrypts the message through the public key.
[1]”Phishing Techniques | Phishing.org.” [Online]. Available: http://www.phishing.org/phishing-techniques/. [Accessed: 25-Oct-2016].
[2]”The Online Service Message Email Is A Google Account Phishing Scam.,” Facebook Tips, 06-Jun-2011. .
[3]”My Computer: Text message phishing scam,” My Computer. .
[4]”Watch Out For Facebook Phishing Scams | Simple Industries, Inc.” [Online]. Available: http://www.simpleindustries.com/2010/10/tech/watch-out-for-facebook-phishing-scams.html. [Accessed: 20-Feb-2017].
[5]”Ads on popular Search Engine are leading to Phishing Sites.” [Online]. Available: https://www.govcert.admin.ch/blog/16/ads-on-popular-search-engine-are-leading-to-phishing-sites. [Accessed: 20-Feb-2017].
[6]”Ads on popular Search Engine are leading to Phishing Sites.” [Online]. Available: https://www.govcert.admin.ch/blog/16/ads-on-popular-search-engine-are-leading-to-phishing-sites. [Accessed: 28-Oct-2016].
[7]”History of Phishing | Phishing.org.” [Online]. Available: http://www.phishing.org/history-of-phishing/. [Accessed: 25-Oct-2016].
[8]L. Meleney, “Dyre Malware Has Stolen Over $1 Billion: Is Your Company’s Sensitive Data at Risk?” [Online]. Available: http://blog.baymcp.com/blog/dyre-malware-has-stolen-over-1-billion-is-your-companys-sensitive-data-at-risk. [Accessed: 20-Feb-2017].
[9]”Dyre Malware Has Stolen Over $1 Billion: Is Your Company’s Sensitive Data at Risk?” [Online]. Available: http://blog.baymcp.com/blog/dyre-malware-has-stolen-over-1-billion-is-your-companys-sensitive-data-at-risk. [Accessed: 28-Oct-2016].
[10]”Phishing prevention with Password Alert FAQ – G Suite Administrator Help.” [Online]. Available: https://support.google.com/a/answer/6197508?hl=en. [Accessed: 20-Feb-2017].
[11]”Password Alert.” [Online]. Available: https://chrome.google.com/webstore/detail/password-alert/noondiphcddnnabmjcihcjfbhfklnnep. [Accessed: 28-Jan-2017].
[12]R. D. Vines, Phishing: Cutting the Identity Theft Line. John Wiley & Sons, 2005.
[13]”Saudi Arabia warns on cyber defense as Shamoon resurfaces | Reuters.” [Online]. Available: http://www.reuters.com/article/us-saudi-cyber-idUSKBN1571ZR. [Accessed: 11-Feb-2017].
[14]”What Is SSL (Secure Sockets Layer)? | DigiCert.com.” [Online]. Available: https://www.digicert.com/ssl.htm. [Accessed: 12-Feb-2017].
[15]”HTTP to HTTPS | What is a HTTPS Certificate.” [Online]. Available: https://www.instantssl.com/ssl-certificate-products/https.html. [Accessed: 12-Feb-2017].
ACADEMIC HONESTY DECLARATION
I, the undersigned, declare that the attached assignment/project is wholly my own work, and that no part of it has been:
- copied by manual or electronic means from any work produced by any other person(s), present or past,
- produced by several students working together as a team (this includes one person who provides any portion of an assignment to another student or students),
- produced by automatic tools or aids
- modified to contain falsified program output,
- or copied from any other source including web sites,
- except as directly authorized by the instructor.
I understand that penalties for submitting work which is not wholly my own, or distributing my work to other students, may result in penalties.
Full name:
Student Number:
___________________
Signature